Surface Go Dual Boot Secureboot
Preface: #
The goal of this guide is to have Windows 10 and Ubuntu installed on a Surface device (I've tested this on the Go and should work the same on the Go2),
with secureboot enabled for both of them.
The version used in this guide are:
- Win10 20H2 Pro (Pro has full bitlocker support)
- Ubuntu Mate 20.04.1 LTS
Prerequisites: #
- disabling Fast Startup:
- in: Control Panel --> hardware and Sound --> Power Options --> System Settings
select "Choose what the power buttons do"
and then unlock the buttons on the bottom clicking on "Change Settings that are not curently available"
and deselect "Turn on gast start-up (recommended)"
then click on "save changes"
- in: Control Panel --> hardware and Sound --> Power Options --> System Settings
- surface Device installed with Win10
- usb pen with Ubuntu 20.04 on it:
- you should create the drive downloading the ISO and dd'ing it on the drive:
dd if=ubuntu.iso of=/dev/sdX bs=1M status=progress,
in this way you are shure to have a UEFI boot drive
I've used Ubuntu Mate 20.04.1 LTS
- you should create the drive downloading the ISO and dd'ing it on the drive:
- patience
Win10 pre-tasks: #
If enabled, disable bitlocker from Win10 bitlocker menu,
wait for the decryption to finish.
Shrink the windows partition form the disk manager to leave space for ubuntu.
Reboot in advanced mode to boot from the USB drive with ubuntu:
hold "shift" while clicking on "reboot",
you'll be in windows recovery mode, select "other disk" and select "Linpus ..." to boot in ubuntu
Ubuntu Live tasks: #
Shrinking: #
fire up utubntu live and with gparted move Win10's recovery partition back to leave all the empty space in the end:
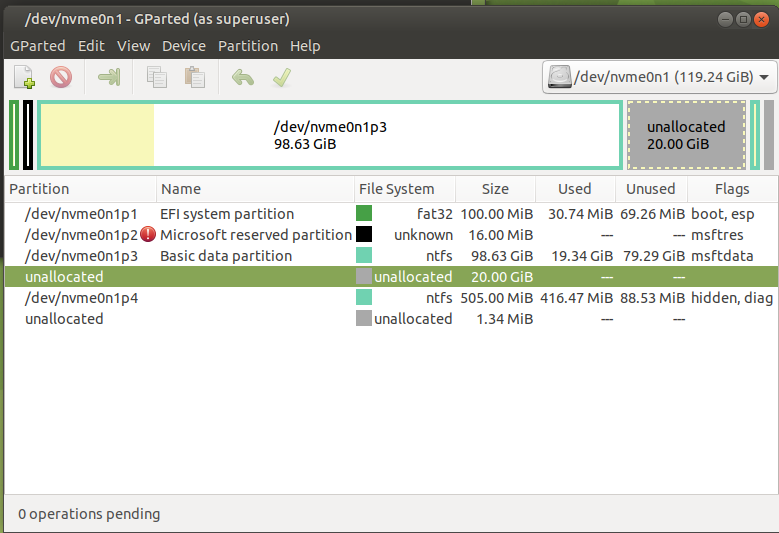
before:
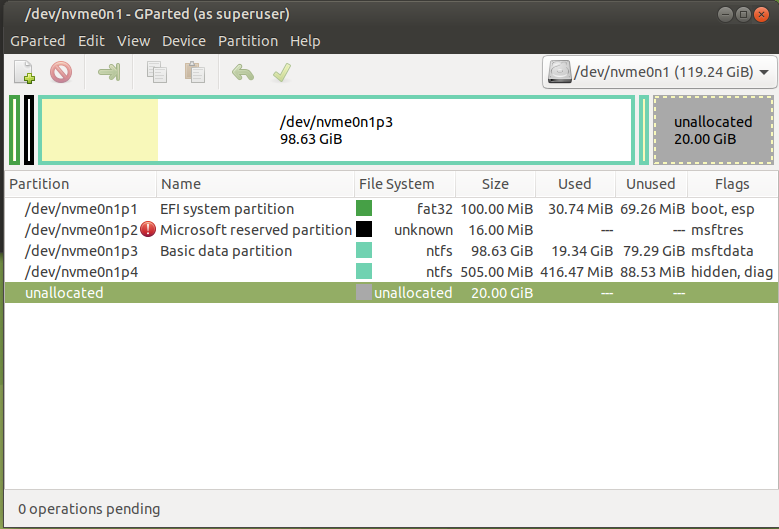
after:
Partitioning: #
with gparted create the new partitions as follows:
5: efi partition in fat32, flags boot and esp (will be mounted on /boot/efi)
6: /boot partition in ext2 (will be mounted on /boot)
7: luks partition
Number Start End Size File system Name Flags
1 1049kB 274MB 273MB fat32 EFI system partition boot, esp
2 274MB 408MB 134MB Microsoft reserved partition msftres
3 408MB 95,1GB 94,7GB ntfs Basic data partition msftdata
4 95,1GB 96,1GB 1074MB ntfs Basic data partition hidden, diag
5 96,1GB 96,7GB 537MB fat32 EFI System Partition boot, esp
6 96,7GB 97,2GB 537MB ext2
7 97,2GB 128GB 30,8GB
Luks: #
format the 7th partition that we'll use with luks:
cryptsetup luksFormat /dev/nvme0n1p7
cryptsetup luksOpen /dev/nvme0n1p7 CRY_main
pvcreate /dev/mapper/CRY_main
vgcreate VG_main /dev/mapper/CRY_main
lvcreate -L 15G -n LV_root VG_main
lvcreate -L 2G -C y -n LV_swap VG_main
vgchange -a yformat the EFi partition:
mkfs.vfat /dev/nvme0n1p5Ubuntu installer: #
now fire up the ubuntu common installer from the desktop icon,
and continue with the normal selection:
- minimal installation
- download updates while installing ubuntu mate
- install third party software...
- configure secureboot
- choosing a password of your choosing
- configure secureboot
the last part is very important since it will allow you to enroll the newly created MOK key in the machine's UEFI
in the partitioning part do:
- select efi nvme0n1p5 and select "Use as" "EFI System Partition"
- select boot nvme0n1p6 and select "Use as" "ext2" and mount on /boot, do format
- select /dev/mapper/VG_main-LV_root "Use as" "ext4" and mount on /
- select /dev/mapper/VG_main-LV_swap "Use as" swap
- select install the bootloader on the efi partition: nvme0n1p5
and continue the installation
DO NOT REBOOT
DO NOT REBOOT
DO NOT REBOOT
Post-installation tasks: #
once finished do not reboot,
mount the newly created system on /mnt creating the environment for chrooting correctly:
mount /dev/mapper/VG_main-LV_root /mnt
mount /dev/nvme0n1p6 /mnt/boot
mount /dev/nvme0n1p5 /mnt/boot/efi
mount --bind /dev /mnt/dev
mount -t proc proc /mnt/proc
mount -t sysfs sys /mnt/systhen chroot in to the newly prepared folder:
chroot /mntIn the chroot: #
blkid | grep -i lukstake the field "UUID"
ES:
/dev/nvme0n1p7: UUID="11111111-2222-3333-4444-555566667777" TYPE="crypto_LUKS" PARTUUID="aaaaaaaa-bbbb-cccc-dddd-eeeeffffaaaa"
in this case it's: 11111111-2222-3333-4444-555566667777
edit the file /etc/crypttab (if not present create)
and add:
CRY_main UUID=11111111-2222-3333-4444-555566667777 none luks,discard
NOTE: the name shall be the same as you opened the crypt device in steps
then recrate the system boot environment:
grub-install
update-initramfs -u -k alland exit the chroot with a simple
exitnow you can reboot your system.
be very aware of the next steps!
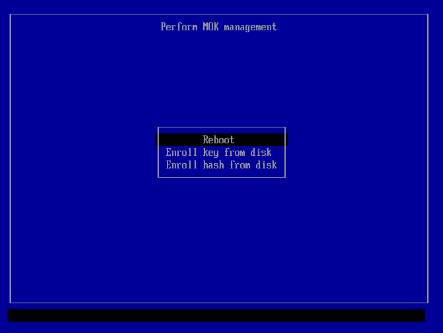
Enrolling MOK Key to Secureboot: #
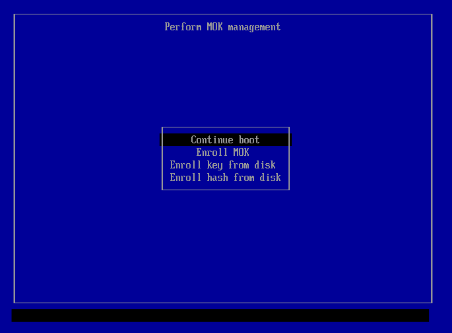
you will be greeted by the UEFI Key manager, where you will be able to enroll the new key for secureboot:
choose "Enroll MOK"
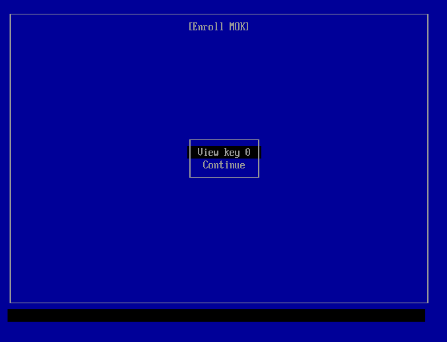
then "continue"
select "Yes"
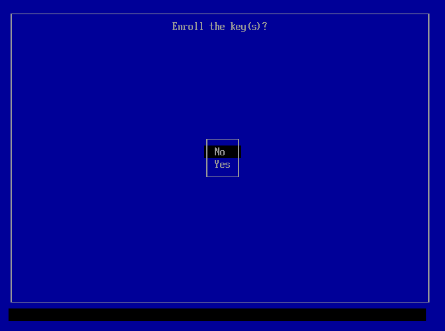
then insert the password you selected during ubuntu installation
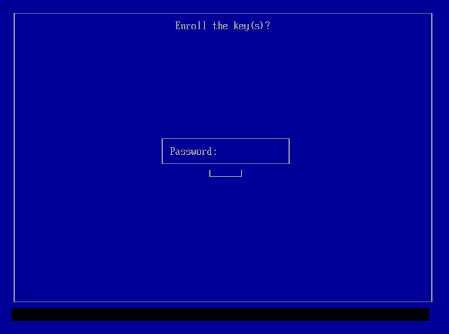
and then select "reboot"
After the reboot: #
now the system should restart and you should be greeted by grub's selection screen,
there you can choose to boot in Ubuntu or in Windows (which has been detected by the installer)
Re-activating bitlocker #
after booting to windows you can re-activate bitlocker,
maybe setting a custom passphrase at boot so your system won't load automatically without your input.
see: Win10 - Surface Go - Bitlocker with TPM and advanced pin